Tech Trends and Solutions
Get the latest insights, trends, and innovations in the ever-evolving world of technology.
- IT Management, IT Security
Selecting the Best Virtual Private Network (VPN) for Your Business
A virtual private network (VPN) is an essential piece of your cybersecurity strategy. Using a VPN allows you to securely connect to your business network

- Maintenance, Technology
Why Your Business Should Have a UPS System
Not only are power outages inconvenient, did you know they can also damage your technology? It is important to protect your equipment with an uninterrupted

- IT Management
Selecting the Best Internet Plan for Your Business
Businesses of all sizes and in all industries depend on a robust internet connection with reliable speeds. There are a wide variety of internet plans

- Phone / VoIP
Is VoIP Phone Service Right for Your Business?
Making voice calls via the internet instead of traditional phone lines is known as Voice over Internet Protocol (VoIP). As a business owner, you are

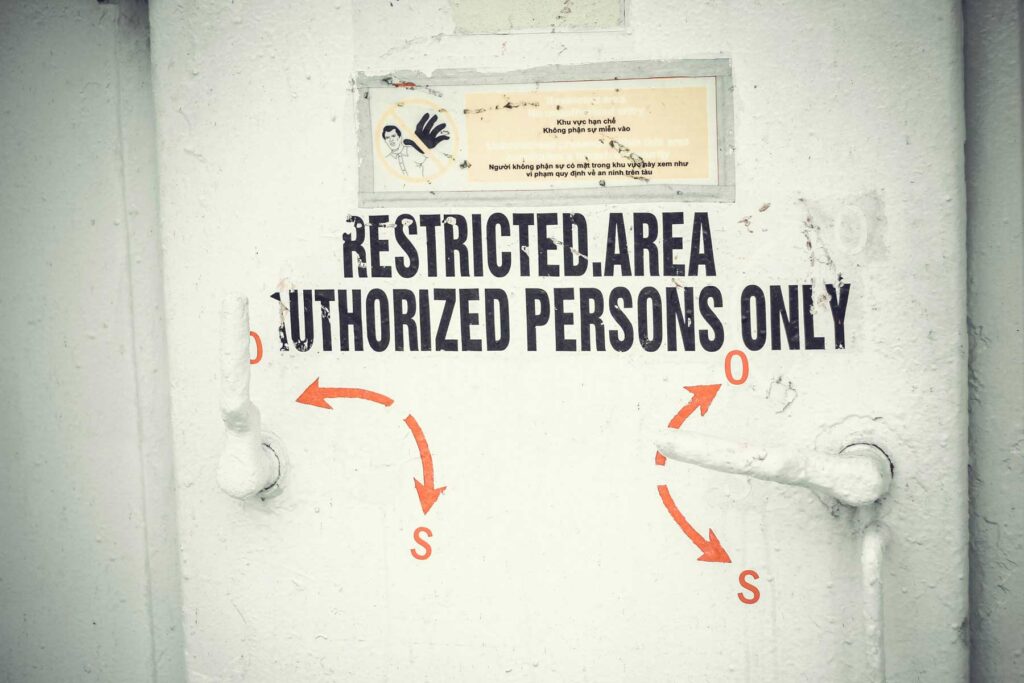
- IT Security
How Strong Authentication Procedures Can Protect Your Business
The cyber world requires businesses to take steps to protect their data from malicious access. There are a range of tools you can use to
- IT Management
Does Your Business Need Managed IT Services?
Information technology (IT) is a significant part of business operations in today’s high-tech society. Small business owners are always looking for ways to increase efficiency,

- IT Management
Do You Need an Outside IT Services Partner?
Small and medium-sized businesses (SMBs) rely on technology to keep the business running efficiently but IT might not be one of your strongest skills. Just

